Penetration Testing
CybersecurityNext Generation Pen Testing
In a time where news of data breaches are becoming “the new normal,” the need for organizations to evaluate their overall risk and avoid becoming the next victim has become critical. Organizations simply can’t protect themselves from risks they’re unaware of. Additionally, many organizations are simply unsure where to start.
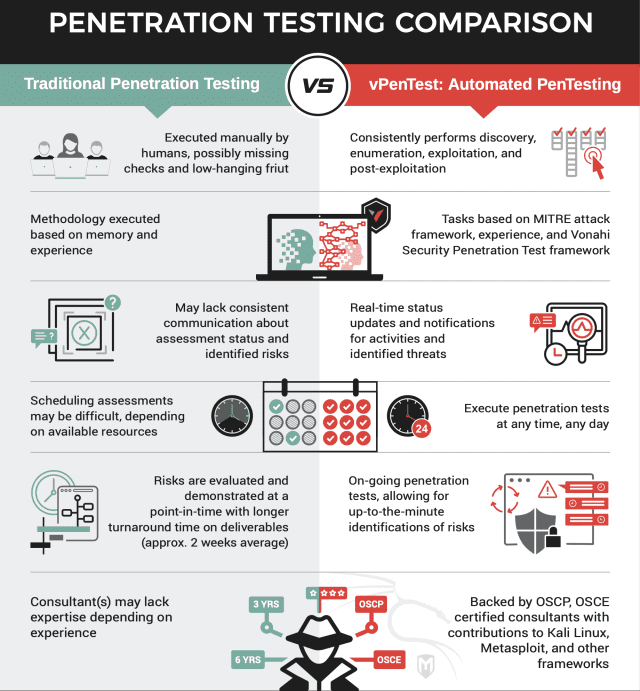
As the demand for cybersecurity consulting services increases, consulting firms are experiencing many difficulties with filling in the roles to provide these services. Many gaps are introduced in the assessments provided to organizations. During a time where attackers are becoming more sophisticated and performing these attacks on a regular basis, it is imperative that organizations establish and maintain an information security program that allows them more flexibility on when and how often they can assess their environments.
HOW vPENTEST HELP SOLVE INDUSTRY CHALLENGES
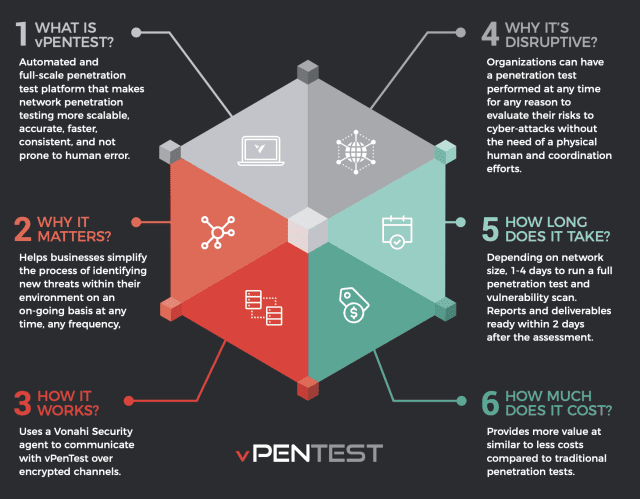
1. vPenTest can run at any time and any frequency.
This essentially means you never have to wait on anyone to perform a penetration test. Technically, you could have a penetration test performed and have the report in your hand by the end of the week, and this is obviously something that cannot happen very easily when it comes to traditional engagements.
2. Real-time Notifications
Notifications are always sent out when the penetration test starts and stops, keeping important individuals in the know as to when things are going on. This is also helpful in case there are some alerts that get triggered.
3. Reports that Drive Results
Considering vPenTest has a reporting framework that is built around quality – the data provided in the reports will always be very informative. How these risks affect your organization, where your organization stands compared to its peers, how this compares to the last assessment, etc. are all examples of data that are included in each report.
4. Cost
The price of vPenTest is very competitive when compared to traditional penetration tests but provides a lot more value for the same or smaller price point.
5: Transparency at Your Fingertips
Customers can always log into their portal to get a list of contacts involved in the project, communicate with the consultant, as well as get a progress update that provides preliminary results and expected completion dates.
6. Reduce Turnaround Time for Detection and Response
Because all activities are tracked, including any manual activities conducted by a consultant, organizations can download this activity log and correlate activities with their SIEM and incident response procedures. This is extremely useful in helping organizations make adjustments and tweak their controls, reducing the turnaround time for detection and response.